admin 发布的文章
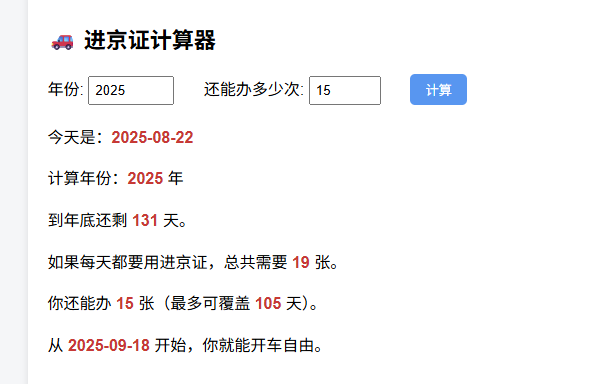
搞了个进京证计算器。
typecho支持EMOJI
刚才发一份代码的时候,提示Database Query Error
通过在config.inc.php添加:
/** 开启Debug模式 */
define("__TYPECHO_DEBUG__",true); 打开调试模式,发现是由于utf8,而不是utf8mb4,导致无法添加代码中的emoji表情。
直接数据库执行:
alter table typecho_comments convert to character set utf8mb4 collate utf8mb4_unicode_ci;
alter table typecho_contents convert to character set utf8mb4 collate utf8mb4_unicode_ci;
alter table typecho_fields convert to character set utf8mb4 collate utf8mb4_unicode_ci;
alter table typecho_metas convert to character set utf8mb4 collate utf8mb4_unicode_ci;
alter table typecho_options convert to character set utf8mb4 collate utf8mb4_unicode_ci;
alter table typecho_relationships convert to character set utf8mb4 collate utf8mb4_unicode_ci;
alter table typecho_users convert to character set utf8mb4 collate utf8mb4_unicode_ci;然后config.inc.php里面更改连接字符集:
'charset' => 'utf8mb4',就好了。
视频文件添加时间戳
行车记录仪导出的视频,没有时间戳。
于是想用ffmpeg添加时间戳。
脚本如下:
#!/bin/bash
set -e
print_help() {
echo "🚗 视频时间戳添加工具(行车记录仪效果)"
echo ""
echo "用法:"
echo " ./timestamp_video.sh"
echo ""
echo "执行后会交互式要求:"
echo " 1. 输入视频文件路径"
echo " 2. 输入该视频的起始北京时间(格式如 2025-06-30 08:00:00)"
echo ""
echo "要求:"
echo " - 系统应安装 ffmpeg"
echo " - 字体路径可自行修改为本地可用 .ttf / .ttc"
echo ""
echo "输出:"
echo " 与原视频同目录,添加 '_with_ts.mp4' 的新文件"
}
if [[ "$1" == "--help" || "$1" == "-h" ]]; then
print_help
exit 0
fi
# === 获取输入 ===
read -rp "📼 请输入视频文件路径(如 input.mp4): " INPUT
if [ ! -f "$INPUT" ]; then
echo "❌ 文件不存在:$INPUT"
exit 1
fi
read -rp "⏰ 请输入起始北京时间(如 2025-06-30 08:00:00): " START_TIME
START_TS=$(TZ="Asia/Shanghai" date -d "$START_TIME" +%s 2>/dev/null || true)
if [ -z "$START_TS" ]; then
echo "❌ 时间格式错误,请使用 YYYY-MM-DD HH:MM:SS 格式"
exit 1
fi
# === 参数配置 ===
DELTA_TS=$((START_TS + 8 * 3600))
FONT="simsun.ttc" # 可替换为你喜欢的中文字体
FONT_SIZE=24
FONT_COLOR="white"
BOX_COLOR="0x00000099"
X_POS=10
Y_POS=10
OUTPUT="${INPUT%.*}_with_ts.mp4"
# === 执行命令 ===
echo "🚀 正在为 $INPUT 添加时间戳..."
ffmpeg -i "$INPUT" -vf \
"drawtext=fontfile='$FONT':
text='%{pts\\:gmtime\\:$DELTA_TS}':
fontcolor=$FONT_COLOR:
fontsize=$FONT_SIZE:
x=$X_POS:y=$Y_POS:
box=1:boxcolor=$BOX_COLOR" \
-codec:a copy "$OUTPUT"
echo "✅ 添加完成:$OUTPUT"